Identity verification started to gain importance over the years, as identity fraud attempts increased in recent years. Fraudsters tend to get away with stealing a company’s data by masking their online presence with someone else’s identity. It not only puts organizations at financial risk but also customers feel insecure during online shopping. Despite the world becoming more digital with each passing day, users are interacting more in real-time with less face contact.
To drive a company’s revenue with an authentic customer base, it’s important to conduct customer identity verification against various forms of identification. Organizations can use any identity ranging from a driver’s license, social security card, a passport to a national identity card. However, either one of these identifications must be a photo ID. But this depends on the organization to choose which identification is sufficient to provide them with a level of assurance required. Contrary to manual identity verification, an automated online identity verification system validates users in real-time within a few seconds or minutes.
Turns out most organizations don’t know how to properly use identity verification systems. How it helps with mitigating the risks and serves to provide a seamless customer onboarding experience. So, the question is, “How do we perform identity verification?”
Verification Identity Coupled with Various Authentication Methods
Before performing digital identity verification, the organizations should first know about different verification methods like address verification, document authentication, biometric validation, etc. Because identity verification is a combination of all these verification methods that help companies to validate a person’s identity from several validation points.
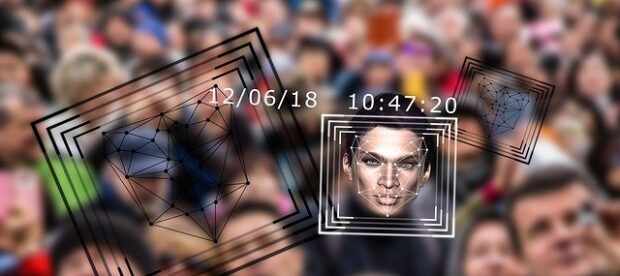
By using an advanced identity verification system, the system detects a person’s unique traits and validates if a person is who they are claiming to be. However, identity verification identity systems are not a single system but it leverages the capabilities of different verification systems to get reliable results. The automated verification system has proven to be quite effective than an old or outdated system.
Meeting Compliance Requirements with Online Identity Verification
Companies can ensure their compliance with KYC and AML regulations by asking their customers to follow a few simple steps for identity verification. Customers could validate their identities by sitting remotely through an automated identity verification system. The system scans through each customer and automatically starts a swift and highly accurate vetting process. Therefore, the verification helps to streamline the customer onboarding process and ensures the honesty of customers.
Verifying Users with Customer Identity Verification
Capture
- Users could easily access the verification system that requires customers to scan either one or more identification documents by accessing the device’s camera.
- Customers can use any government-issued ID document like passport, national identity card or driver’s license, etc to provide proof of their address. Furthermore, it also helps organizations to adhere to KYC and AML regulations.
- The initial ID document used for capturing the customer information should have that person’s image.
Analyze
- The system uses the customer selfie to conduct facial biometric Further, the information is stored inside the system’s large database.
- With a facial biometric authentication system, the technology automatically compares the person’s selfie with a photograph on an identity document.
- The system also conducts liveness detection to check if the user appears to be himself or someone else.
Verify
- By conducting different risk management and threat detection features, the system automatically compares the personal and biometric data against a large database. For instance, the system would check for the expiration date and match the username with a known address.
- During the risk assessment process, the system extracts different data points like the type of device, geolocation, including behavioral biometrics that enrich the individual’s profile.
- Moreover, the system uses fingerprints and automatically detects irregularities in device settings like geo-location. The system automatically uses the data and compares it against different watchlists like Politically Exposed Persons (PEP’s) Lists to check the person’s background.
Read More: F95Zone
Conducting Comprehensive Check with Identity Verification System
- The system automatically updates and stores information related to identity documentation, analysis, and authentication data.
- Organizations like banks or financial institutions gain a comprehensive customer due to diligence reports to help them monitor the customer’s activity. Moreover, it helps entities to comply with the KYC process.
- However, the system continues to track the customer’s online activity to assess risks and threats attached with ongoing monitoring.
The automated identity verification solution can help save company’s both time and money during the vetting process. During this process, the individual isn’t standing before a person to authenticate their identity by showing a photo ID document. Through an automated solution, the system conducts several authentication techniques to validate the user’s identity.